| Support Vector Machines w/ JAVA & SMO (Sequential Minimal Optimization) |
| prototypeprj.com = zaneacademy.com (version 2.0) |
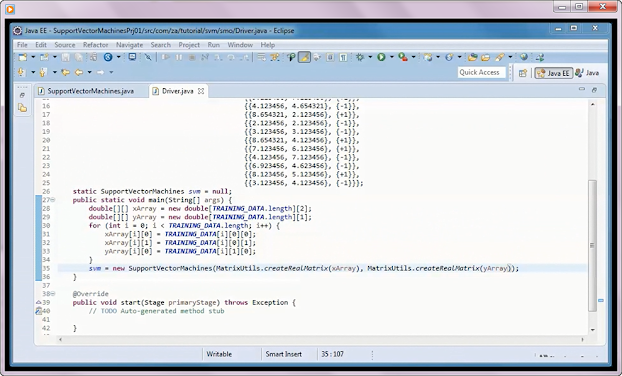
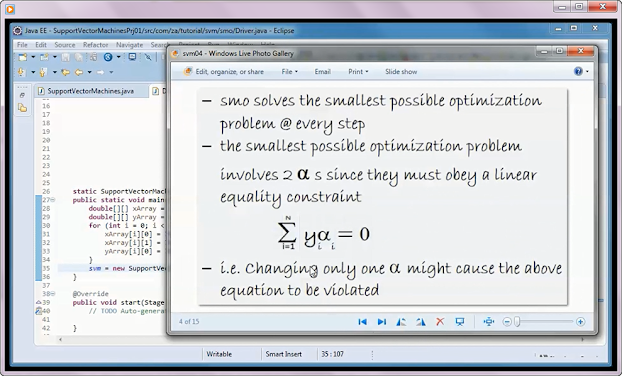
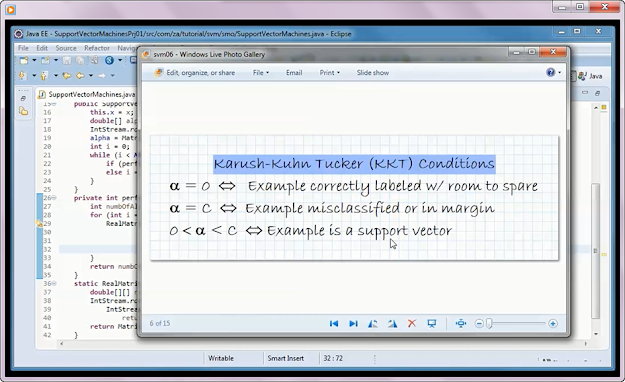
00:07 demo a prebuilt version of the application 01:50 code the application 02:11 go over the various classes that make up the app. 03:08 go over the training data used in this app. 03:52 setup and use the commons math jar to do matrix operations 04:33 start the initial coding of the SupportVectorMachines class 05:20 quick introduction to Support Vector Machine (SVM) 06:46 quick introduction to Sequential Minimal Optimization (SMO) 07:50 resume coding the application SupportVectorMachines class 09:41 plug in equation for 'w' into equation of a linear svm and use resulting equation in code 10:40 EPSILON and slack penalty C 11:02 alpha and the violation of KKT conditions 11:54 selecting the index of the 2nd alpha to optimize 13:26 optimize an alpha pair and b 15:15 define and calculate w 15:37 classify method 16:12 display information tables code 16:54 handle command line entry code 17:12 JavaFX display code 18:14 explain + test run the application 19:27 change C and rerun app. to show overfitting ----------------------------------------------------------------------------------------------------------------------------- quickly download, import into Eclipse, and run zip file for 'Support Vector Machines w/ JAVA & SMO (Sequential Minimal Optimization)' ------------------------------------------------------------------------------------------------------------------------------- ----------------------------------------------------------------------------------------------------------- download source code @https://sites.fastspring.com/prototypeprj/instant/ai ----------------------------------------------------------------------------------------------------------- |
Labels
ACO
(3)
AdaBoost
(2)
Ant Colony Optimization
(2)
Backpropagation
(2)
binary constraint graph
(1)
blockchain
(2)
brute force
(1)
brute force algorithm
(1)
Class Scheduling
(12)
conditional independence
(1)
conference cheduling
(1)
conference scheduling
(2)
constraint satisfaction problem
(3)
cryptocurrency
(3)
csp
(3)
cyclic group
(1)
data mining
(3)
decision trees
(12)
derive equations
(1)
DHKE
(6)
Diffie Hellman Problem
(1)
Diffie-Hellman Key Exchange
(2)
Digital Signature Algorithm
(1)
Discrete Logarithm Problem
(1)
double and add algorithm
(1)
download source code
(1)
DSA
(1)
ecc
(1)
ECDH
(1)
ECDSA
(1)
Elgamal
(1)
Elgamal Digital Signature
(1)
Elliptic Curve
(1)
Elliptic Curve Diffie–Hellman key exchange
(1)
Elliptic Curve Cryptography
(1)
Elliptic Curve Digital Signature Algorithm
(1)
Encryption
(1)
euler phi function
(1)
extended euclidean algorithm
(1)
generalized discrete logarithm problem
(1)
generate rules
(3)
Genetic Algorithm
(5)
Genetic Algorithms
(19)
gradient descent
(2)
group
(1)
group generator
(1)
grow xml tree
(1)
Handle Underflow
(1)
hashing
(1)
hill climbing
(7)
hopfield network
(2)
independence
(1)
info gain
(1)
information gain
(2)
java
(84)
javafx
(1)
k-nearest neighbors
(2)
Laplace Smoothing
(2)
linear algebra
(3)
Linear Regression
(2)
logical operators
(1)
logistic regression
(4)
map coloring
(1)
message authenticity
(1)
message confidentiality
(1)
message integrity
(1)
multi-party Diffie-Hellman Key Exchange
(1)
Naive Bayes
(6)
nearest neighbor
(1)
nearest neighbors
(1)
Neural Networks
(10)
node splitting
(1)
Normal Equation
(2)
numpy
(1)
P2P
(10)
Peer to Peer
(5)
peer-to-peer
(2)
point addition
(1)
point doubling
(1)
pow
(3)
probability
(2)
proof of work
(3)
proof-of-work
(1)
public key cryptography
(9)
Public Key Cryptography + DHKE w/ Encryption + JAVA
(1)
Python
(18)
random restart hill climbing
(2)
robotics
(1)
rsa
(1)
RSA Digital Signature
(1)
Scala
(1)
Sentiment Classification
(4)
Sequential Minimal Optimization
(2)
sha-256
(1)
simulated annealing
(2)
SMO
(2)
sqlite
(21)
stochastic gradient descent
(2)
Support Vector Machines
(2)
SVM
(2)
Traveling Salesman Problem
(1)
TSP
(13)
underflow handling
(1)
use rules
(3)
workshops scheduling
(2)
Blog Archive
-
▼
2020
(98)
-
▼
July
(27)
- Public Key Cryptography + Elgamal Encryption Schem...
- Public Key Cryptography + DHKE w/ Encryption + JAVA
- Class Scheduling Application (03) + Genetic Algori...
- Public Key Cryptography + Elgamal Digital Signatur...
- Neural Networks + JAVA + Backpropagation 02
- Digital Signature Algorithm (DSA) - Public Key Cry...
- Elliptic Curve Diffie–Hellman key exchange (ECDH)...
- AdaBoost w/ JAVA
- TSP + Ant Colony Optimization (ACO) + SQLite DB + ...
- RSA w/ JAVA
- Elliptic Curve Digital Signature Algorithm (ECDSA)...
- Support Vector Machines (SVM) w/ Sequential Minima...
- Decision Trees + build xml decision trees + JAVA +...
- Genetic Algorithms w/ Scala - Tutorial 01
- Class Scheduling w/ Genetic Algorithms and Python
- Ant Colony Optimization (ACO) + JAVA + Traveling S...
- RSA Digital Signature w/ JAVA
- Peer to Peer (P2P) w/ JAVA
- AdaBoost w/ Python
- Linear Regression w/ Java & Normal Equation (01)
- Derive equations For point addition & point doubl...
- Support Vector Machines (SVM) w/ JAVA & Sequential...
- Sentiment Classification w/ Naive Bayes + JAVA + L...
- Elliptic Curve Cryptography (ECC) - Public Key Cry...
- Backpropagation w/ JAVA (01) - Neural Networks (09)
- Diffie-Hellman Key Exchange - Public Key Cryptogra...
- PrototypePrj.com Core Values
-
▼
July
(27)
Tuesday, July 14, 2020
Support Vector Machines (SVM) w/ JAVA & Sequential Minimal Optimization (SMO)
Subscribe to:
Post Comments (Atom)

























No comments:
Post a Comment